Microsoft Graph authentication
Introduction to Microsoft Graph authentication
This chapter describes the required steps to connect to Microsoft Graph webservices (Azure, Office 365, Microsoft 365). Detailed information about Microsoft Graph can be found here: https://docs.microsoft.com/en-us/graph/.
The different types of permissions for Microsoft Graph are explained here . To get access to the API without a user's credentials, Application permissions are used.
To access Microsoft Graph using Application permissions, first follow the instructions on this page to configure the app registration, which is required to retrieve an authorization token.
Process flow
Once you have set up your app registration in the Azure portal, you can create a process flow to authenticate and call the required services.
In this example we will be using the following process flow, which is triggered by the execution of a task, then uses an HTTP connector to authenticate and get an authorization token, calls a Graph web service using that token, and shows the response of that call. Only the two HTTP connector actions are described here.
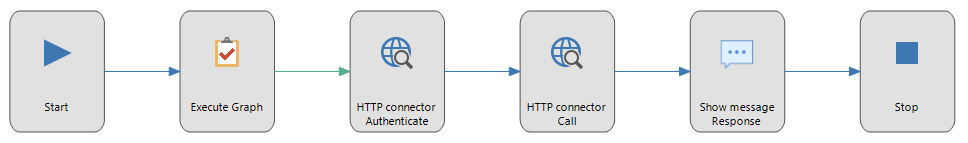 Example process flow
Example process flow
The process flow uses three process variables, token, header and response, all of type nvarchar(max).
HTTP connector: Authenticate
The authentication process action retrieves an authorization token required to access the web service.
Input
The input parameters of the process action should be configured like this:
| Input parameter | Assignment | Value |
|---|---|---|
| URL | Constant value | https://login.microsoftonline.com/{tenant}/oauth2/v2.0/token |
| HTTP method | Constant value | POST |
| Content-Type | Constant value | application/x-www-form-urlencoded |
| Content | Constant value | client_id={client id}&scope=https%3A%2F%2Fgraph.microsoft.com%2F.default&client_secret={client secret}&grant_type=client_credentials |
The tenant, client id and client secret for the registered app can be found in the Overview and Certificates & secrets pages of the Azure portal.
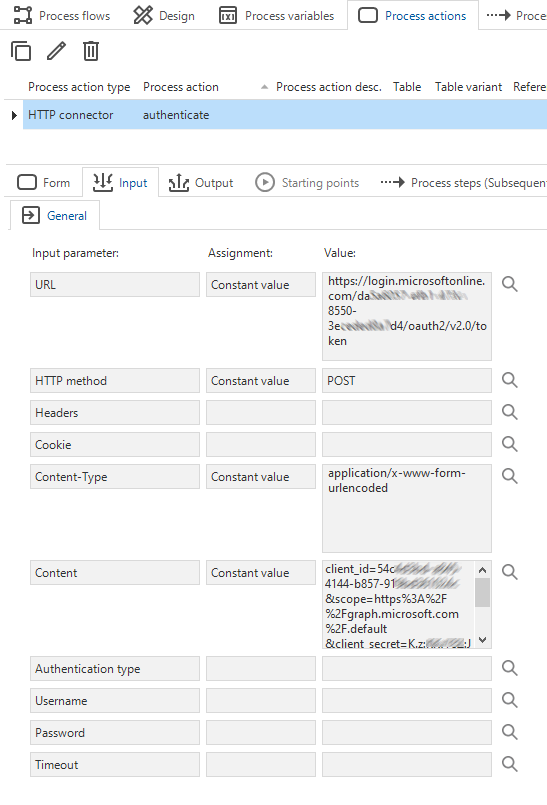 Example HTTP connector input configuration
Example HTTP connector input configuration
Output
The content of the response is stored in the token parameter by mapping it to the Content output parameter.
| Output parameter | Value |
|---|---|
| Content | token |
To extract the authorization token from the response and create the authorization header, add the following code to the process procedure of the authentication action:
set @header = '[{ "Key": "Authorization", "Value": "Bearer '
+ json_value(@token, '$.access_token') + '" }]'
HTTP connector: call web service
The next process action calls the required web service, which in this example is a service to list all groups.
Input
The input parameters of the process action should be configured like this:
| Input parameter | Assignment | Value |
|---|---|---|
| URL | Constant value | https://graph.microsoft.com/v1.0/groups?$select=displayName |
| HTTP method | Constant value | GET |
| Headers | Variable | header |
Output
The output parameter Content should be assigned to the response parameter.
| Output parameter | Value |
|---|---|
| Content | response |
After the call, the response parameter will have the following JSON content:
{
"@odata.context": "https://graph.microsoft.com/v1.0/$metadata#groups(displayName)",
"@odata.nextLink": "https://graph.microsoft.com/v1.0/groups?$select=displayName",
"value": [
{
"displayName": "Business Development"
},
{
"displayName": "Marketing"
},
{
"displayName": "Service & Care"
},
{
"displayName": "Product Innovation"
},
...
]
}
Process the results
To process the results, use the SQL Server json_value and openjson functions, for example:
select json_value(a.value, '$.displayName') as displayName from openjson(@json, '$.value') a
| displayName |
| -------------------- |
| Business Development |
| Marketing |
| Service & Care |
| Product Innovation |